Securing Traction SCADA: A Unidirectional Architecture

Modern railway systems are increasingly data-driven. Energy management systems (EMS), supervisory control and data acquisition (SCADA), and remote terminal units (RTUs) now operate within interconnected digital environments that improve efficiency, monitoring, and operational visibility. At the same time, this connectivity requires carefully engineered segmentation to preserve the integrity of core control systems.
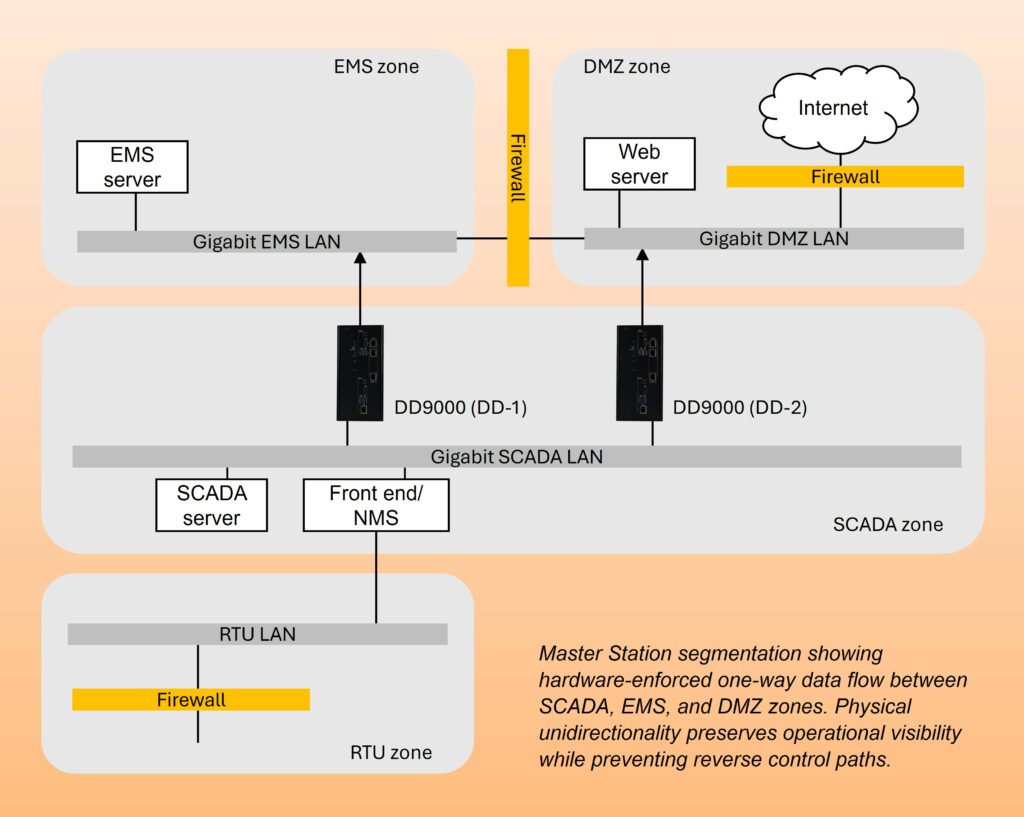
In a recent deployment for one of the world’s major railway networks in South Asia, a unidirectional security architecture was implemented to protect critical traction power infrastructure.
Network Architecture and Security Objective
The railway network structure includes 90 major control centers, linked to over 1,000 assets: signaling systems, control networks, SCADA power systems, control center servers, and surveillance & operational telemetry. To ensure safety, the signaling and control networks must never receive commands from external IT networks, while the SCADA and central systems require real-time log and monitoring data to support operations.
Therefore, the network is segmented into defined security zones:
- RTU Zone – Field data acquisition
- SCADA Zone – Supervisory monitoring and control
- EMS Zone – Energy management and control applications
- DMZ – External connectivity, web servers, signage, display systems
The engineering objective was not to eliminate data sharing, but to allow controlled visibility while preventing reverse communication from lower-trust zones into higher-trust operational systems.
Engineering Approach: Hardware-Enforced One-Way Data Flow
Within a master station network, two DD9000 data diodes are deployed:
- Between SCADA and EMS (DD-1)
SCADA data is transmitted to EMS for supervisory visibility. The physical one-way path ensures that no control, configuration, or command traffic can travel from EMS back to SCADA. - Between SCADA and DMZ (DD-2)
Processed operational data is transmitted outward to web servers and external display systems without exposing the SCADA or EMS core.
The resulting data flow is structured and deterministic:
- RTUs send field data to SCADA servers
- SCADA forwards processed data to EMS via UDD-1
- EMS data is transmitted to DMZ web servers via UDD-2
Because communication is physically unidirectional, no command or configuration traffic can return from the DMZ to SCADA or EMS.
Unlike logical firewall policies, this enforcement is architectural. The absence of a return path eliminates entire categories of remote exploitation risks. A total of 150 data diode units were installed to protect this vast national railway.
Operational Outcomes
The deployment achieved several measurable security and operational goals:
- Absolute isolation of core control systems from external networks
- Mitigation of zero-day exposure risk through hardware-enforced segmentation
- Standards alignment with NERC CIP, ISA/IEC 62443, and ISO 27019 frameworks
- Scaled diagnostic capabilities up to 1Gbps while ensuring that malicious packets could not travel upstream
- Preserved operational visibility while reducing operational overhead, enabling management and external stakeholders to access real-time dashboards remotely, without increasing attack surface
Threat scenarios addressed include malware originating from internet-facing systems, insider misuse of SCADA control paths, and exploitation of web-facing applications. By design, these vectors cannot propagate, either downstream to SCADA or field systems, or up into EMS.
Engineering Perspective
For large-scale infrastructure operators, the question is not whether data should move across zones—it must. The question is how to move it without introducing control-plane exposure.
In this railway deployment, unidirectional gateways were used not as perimeter devices, but as architectural control points within the network core. The result is a segmented design that supports modernization while maintaining deterministic separation of critical control assets.
The mission isn’t just to protect a server; it’s to secure a web of critical assets that define a whole country’s GDP:
- 7,300+ Railway Stations: Each a potential entry point for network intrusion.
- 13,000+ Locomotives: Moving data in real-time that must remain untampered.
- 68,000+ Route Kilometers: A vast physical expanse that requires automated, “set-and-forget” hardware security.
In high-consequence environments such as national transportation systems, security architecture must balance visibility, scalability, and assurance. Hardware-enforced unidirectional communication provides a method of achieving that balance.

