Network Segmentation
|BlackBearの見解:双方向通信は重要な機器設備をリスクにさらす可能性があります。
2017.11.09
One thing that comes up all the time with clients is how to segment their network(s). There’s no simple answer to this, and we often see organizations over- and under-segmenting their environments. My colleague, security guru Greg Young has published our official positions on network segmentation (including microsegmentation) and a few takeaways include:
For starters, the core principle is that segmentation is based on data sensitivity, location and criticality. Further, in virtualized environments, change the technology, but not the security principles. Also, We’ve said it before, but it bears repeating: Don’t Oversegment:
Network segmentation projects are often triggered from an assessment of the network as being overly flat. Flat networks do not have defense in depth, and raise the impact of a successful attack because “all your eggs are in one basket.” The most common mistake Gartner sees being made in response to remedying a flat network is to oversegment, or create too many zones. A principle of network segmentation is to group like resources together, to minimize security overhead: Build a fence around the car park, not a fence and gate around every car.
Greg and I talk pretty regularly, and even though networking and security are fundamentally different, we strongly agree on a common principle: Don’t outsource network design.
Network segmentation projects are usually a rare occurrence in an enterprise, so there is likely to be little experience with staff in conducting them; however, the tendency to seek out a subject matter expert outsourcer to lead the effort should be resisted. Network segmentation decisions are based on internal business, rather than technology knowledge. Most Gartner clients that have outsourced the project have regretted that decision.
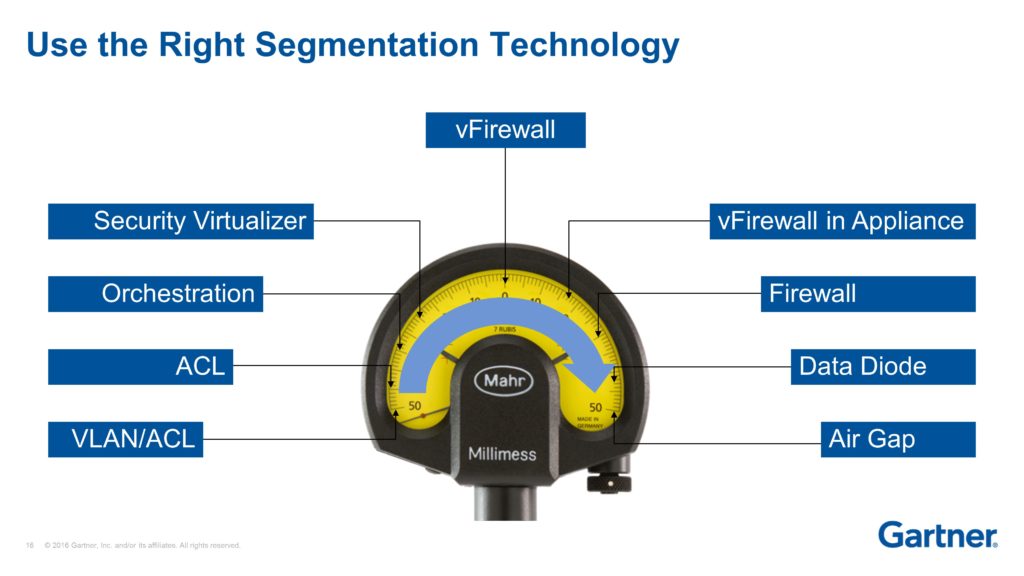
Don’t Cut the Lawn with Scissors: Not all segmentation mechanisms are equal in terms of trust. Mismatches of trust in segmentation result in too little risk, causing unnecessary expense and latency, or too much risk, exposing the enterprise.
You can access the full research here (paywall): Best Practices in Network Segmentation for Security
Summary: Implementing better network segmentation to improve security is a significant project for network operations, data center ops and security teams. From dividing IoT from IT using microsegmentation to avoiding oversegmentation, we call out best practices for maximizing success in this task.
Source: Gartner
Author: Andrew Lerner
(https://blogs.gartner.com/andrew-lerner/2017/11/09/network-segmentation/)
